The Ransomware Recovery Trap: Why Your Backups Aren’t as Safe as You Think
|July 26, 2025Introduction Ransomware is no longer a simple threat; it’s a global criminal enterprise targeting businesses of all sizes. While many organizations believe their backups are an insurance policy against ...Read More - The Ransomware Recovery Trap: Why Your Backups Aren’t as Safe as You Think
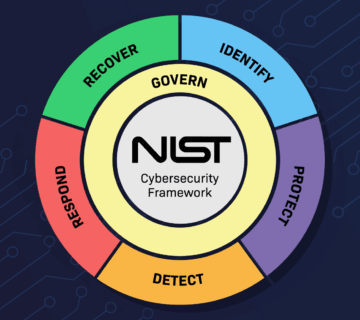
Cybersecurity Frameworks Decoded: Why NIST Is the Backbone of Secure IT Infrastructure
|July 24, 2025Introduction Businesses are under siege. From phishing and ransomware to insider threats and advanced persistent attacks, the digital landscape is brutal. The most damaging part? Most businesses don’t even ...Read More - Cybersecurity Frameworks Decoded: Why NIST Is the Backbone of Secure IT Infrastructure

How AI Voice Spoofing Is Hijacking Businesses
|July 20, 2025Introduction In an age where voice is no longer proof of identity, businesses face an alarming threat: AI-generated voice spoofing. Cybercriminals are now using synthetic voice technology to mimic ...Read More - How AI Voice Spoofing Is Hijacking Businesses

Zero-Port Tunneling: The Future of Cybersecurity Has No Open Ports
|July 14, 2025Introduction Open ports are the digital equivalent of leaving windows cracked open in a fortress. Even with firewalls and intrusion detection, if a port is visible to the internet, it ...Read More - Zero-Port Tunneling: The Future of Cybersecurity Has No Open Ports

The Ransomware Wake-Up Call: Why Cloud Backups Won’t Save You
|July 12, 2025Introduction A ransomware attack is no longer just a worst-case scenario but it’s the new normal. It’s not a matter of if, but when. What’s more ...Read More - The Ransomware Wake-Up Call: Why Cloud Backups Won’t Save You
