
Insider Threats: The Silent Risk in Your Compliance Arsenal
|July 30, 2025Introduction When external threats dominate headlines, many businesses assume the biggest risk lies outside their walls. But internal compromise from careless mistakes or deliberate misuse and is a far more ...Read More - Insider Threats: The Silent Risk in Your Compliance Arsenal

The Compliance Conundrum: Why Unified Standards Are the Future of Cybersecurity
|July 28, 2025Introduction The digital world is crawling with regulations and for good reason. With cyber threats accelerating, businesses must navigate an ever-growing labyrinth of security standards. But what happens when ...Read More - The Compliance Conundrum: Why Unified Standards Are the Future of Cybersecurity
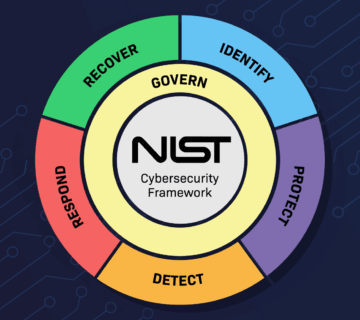
Cybersecurity Frameworks Decoded: Why NIST Is the Backbone of Secure IT Infrastructure
|July 24, 2025Introduction Businesses are under siege. From phishing and ransomware to insider threats and advanced persistent attacks, the digital landscape is brutal. The most damaging part? Most businesses don’t even ...Read More - Cybersecurity Frameworks Decoded: Why NIST Is the Backbone of Secure IT Infrastructure

Data Sovereignty: The Legal Risk You Didn’t Know You Were Taking
|July 10, 2025Introduction Most companies assume their data is safe as long as it's in "the cloud." But what many overlook is where the cloud physically stores that data and who ...Read More - Data Sovereignty: The Legal Risk You Didn’t Know You Were Taking

Why SOC 2 Compliance Matters: Protecting Your Business with Transparent & Secure Infrastructure
|July 6, 2025Introduction SOC 2 compliance isn’t just a checkbox for tech companies; it’s the backbone of trust in modern digital infrastructure. Yet, many businesses still underestimate how damaging a ...Read More - Why SOC 2 Compliance Matters: Protecting Your Business with Transparent & Secure Infrastructure
