
Insider Threats: The Silent Risk in Your Compliance Arsenal
|July 30, 2025Introduction When external threats dominate headlines, many businesses assume the biggest risk lies outside their walls. But internal compromise from careless mistakes or deliberate misuse and is a far more ...Read More - Insider Threats: The Silent Risk in Your Compliance Arsenal

The Compliance Conundrum: Why Unified Standards Are the Future of Cybersecurity
|July 28, 2025Introduction The digital world is crawling with regulations and for good reason. With cyber threats accelerating, businesses must navigate an ever-growing labyrinth of security standards. But what happens when ...Read More - The Compliance Conundrum: Why Unified Standards Are the Future of Cybersecurity
The Ransomware Recovery Trap: Why Your Backups Aren’t as Safe as You Think
|July 26, 2025Introduction Ransomware is no longer a simple threat; it’s a global criminal enterprise targeting businesses of all sizes. While many organizations believe their backups are an insurance policy against ...Read More - The Ransomware Recovery Trap: Why Your Backups Aren’t as Safe as You Think
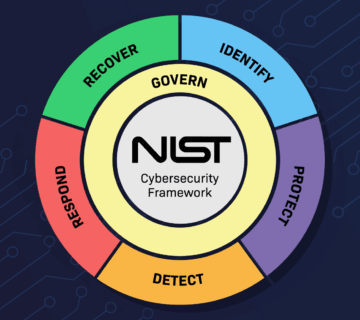
Cybersecurity Frameworks Decoded: Why NIST Is the Backbone of Secure IT Infrastructure
|July 24, 2025Introduction Businesses are under siege. From phishing and ransomware to insider threats and advanced persistent attacks, the digital landscape is brutal. The most damaging part? Most businesses don’t even ...Read More - Cybersecurity Frameworks Decoded: Why NIST Is the Backbone of Secure IT Infrastructure

The Rise of Initial Access Brokers: How Cybercrime is Becoming a Service
|July 22, 2025Introduction Initial access brokers (IABs) are reshaping the cybercrime landscape. These digital middlemen sell stolen access to corporate systems, often paving the way for larger ransomware attacks. Businesses rarely see ...Read More - The Rise of Initial Access Brokers: How Cybercrime is Becoming a Service
[vc_row][vc_column][cz_gap][/vc_column][/vc_row][vc_row][vc_column][cz_posts layout="cz_posts_list_5" title_tag="h1" hover_pos="cz_grid_1_mid tal" icon="" loadmore="pagination" tilt="on" excerpt_rm="true" id="cz_103635" query="" posts_per_page="5" subtitles="%5B%7B%22t%22%3A%22author%22%7D%2C%7B%22t%22%3A%22custom_text%22%2C%22ct%22%3A%22%7C%22%7D%2C%7B%22t%22%3A%22date%22%7D%5D" el="30" sk_readmore="color:#ffffff;font-weight:700;text-transform:uppercase;background-color:#ff0000;padding:10px 40px;border-radius:5px;box-shadow:1px 1px 21px 1px rgba(0,0,0,0.2);" sk_readmore_hover="color:#ff0000;background-color:#ffffff;" sk_img="border-radius:5px;box-shadow:1px 1px 21px 1px rgba(0,0,0,0.2);" sk_title="text-transform:uppercase;" sk_meta="font-size:16px;text-transform:uppercase;" sk_meta_hover="color:#ff0000;" sk_title_hover="color:#ff0000;" gap="25px" sk_container="margin-top:-25px;margin-bottom:-100px;"][/vc_column][/vc_row][vc_row][vc_column][cz_gap][/vc_column][/vc_row]
